 Over these past few months, one of my favorite tools has been ILSpy.
Over these past few months, one of my favorite tools has been ILSpy.
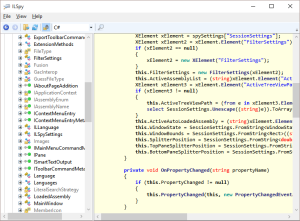
I’ve always had fun trying to reverse engineer applications and figure out how they work, but ILSpy simplifies that quite a bit — at least for .NET applications and libraries.
Since I like investing the effort up-front, so I can be lazier later on, I wrote a simple utility to make using ILSpy even easier for myself. Given a target directory, it drills down into it in order to find all of the .NET-based assemblies. To do that, it attempts a call to System.Reflection.AssemblyName.GetAssemblyName and checks to see if it returns anything. If it does, ILSpy is likely able to decompile the compiled IL code to its more readable (to me) .NET source, so it gets added to my list. Anything else is ignored. This lets me quickly see EXEs or DLLs that are of interest. From there, I can just double-click on the the entry to open it up in ILSpy. Easy-Peasy.
With assemblies not written in .NET, I generally stick to using Strings or maybe some really basic debugger stuff. Those tend to be less useful to me, though, since I’m still pretty weak on the assembly language side of things.
If you haven’t played with a decompiler before, I definitely recommend it. It’s amazing what you can find out, even about commercial applications.
It definitely has opened my eyes to the importance of obfuscation. While it won’t necessarily do a whole lot for someone who is determined to reverse engineer your code, it will at least provide enough of an obstacle to deter the more casual and curious users, like myself ;)